To allow external is able to access workloads hosted on ACVS, you need to configure Destination NAT rule to translate public IP to your internal workload IP . The workload IP runs on NSX logical segment.
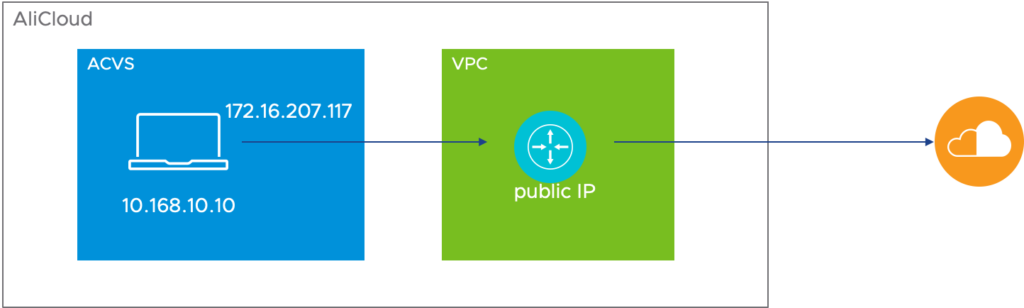
As illustrated in diagram that workloads or virtual machines are connected to VPC before the traffics are being routed to internet. There are going to two IP address translations that first happened in NSX to translate from local IP address in logical segment to a IP that defined by AliCloud which in purpose for NAT. In this example, it is translated from 10.168.10.10 to 172.16.207.117. The 2nd NAT translation is in VPC to a public IP.
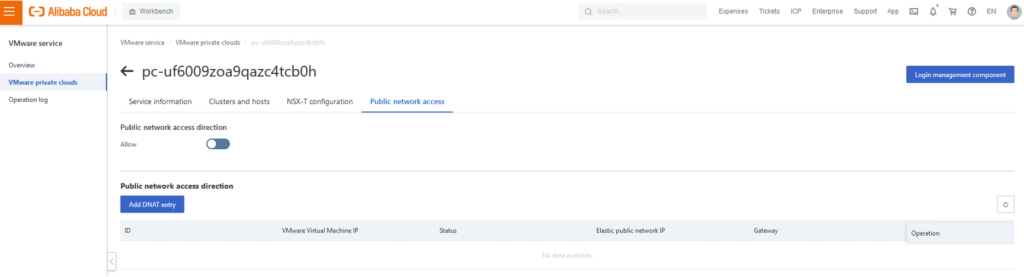
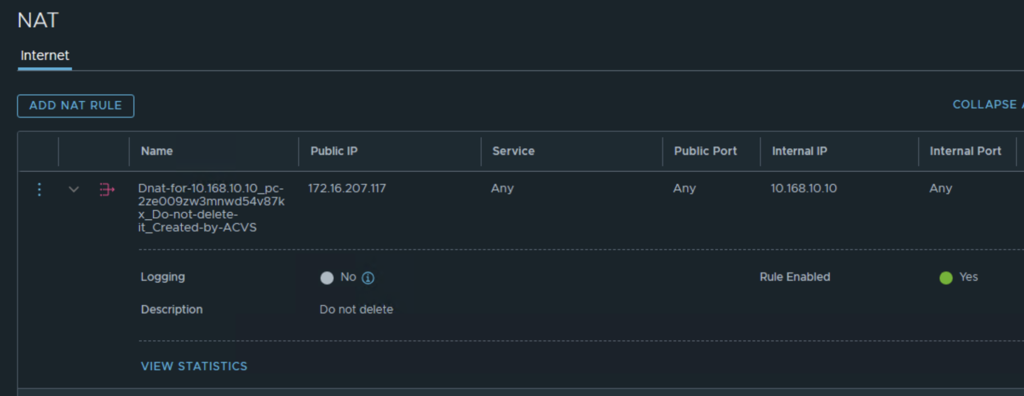
The first NAT rule is configured in NSX, however it is automatically configure by ACVS which when you configure the 2nd NAT. Thus the correct process to do DNAT setting is to start on ACVS console UI. From there when you add a DNAT entry , another DANT entry will be created in NSX with remark “Don Not Delete” in its name.
This rule shows that IP 10.168.10.10 is translated to 172.16.207.117 and doesn’t need you to do anything.
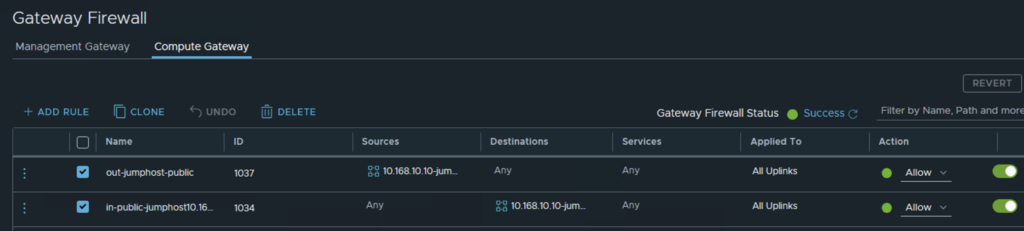
Next to make you traffic can be routed into ACVS, we need to configure firewall rule to allow both ingress and egress from endpoint 10.168.10.10.
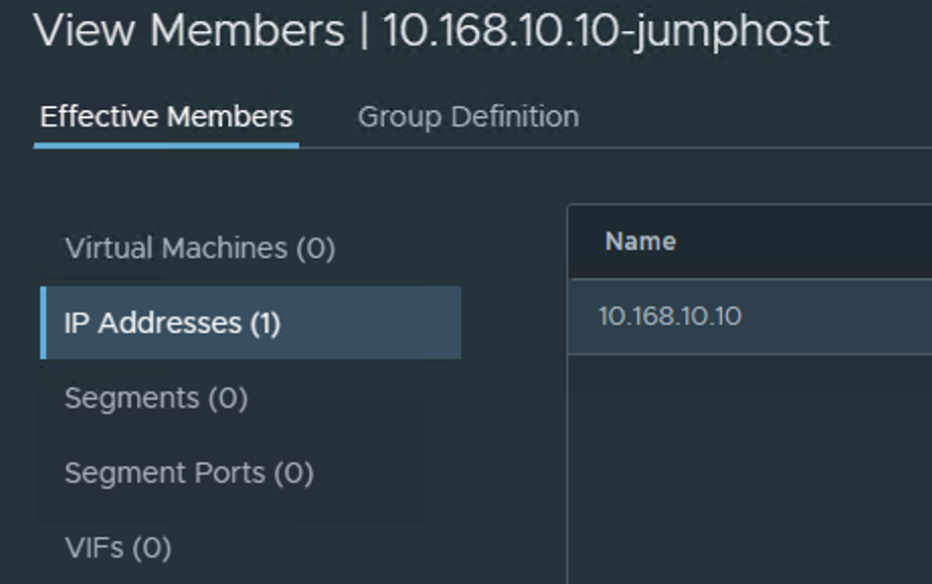
Here I have configured bidirectional rule from 10.168.10.10 to any and from any to 10.168.10.10. In the group I defined the specific IP address is specified.
In conclusion, the DNAT configure on ACVS should only performed on ACVS console. Besides, a firewall rule is needed to allow access from both directions.
