Ransomware attacks have emerged as a significant threat to businesses and applications, making them a top priority for CIO. The impact of ransomware attacks on businesses has escalated widely in recent years that resulting financial losses, operational disruptions, reputation damage, and compromised data security. VMware Cloud Disaster Recovery (VCDR) deliveries enterprise capabilities to support with feature of VMware Ransomware Recovery (RWR) to gain the confidence and speedup the time to recovery.
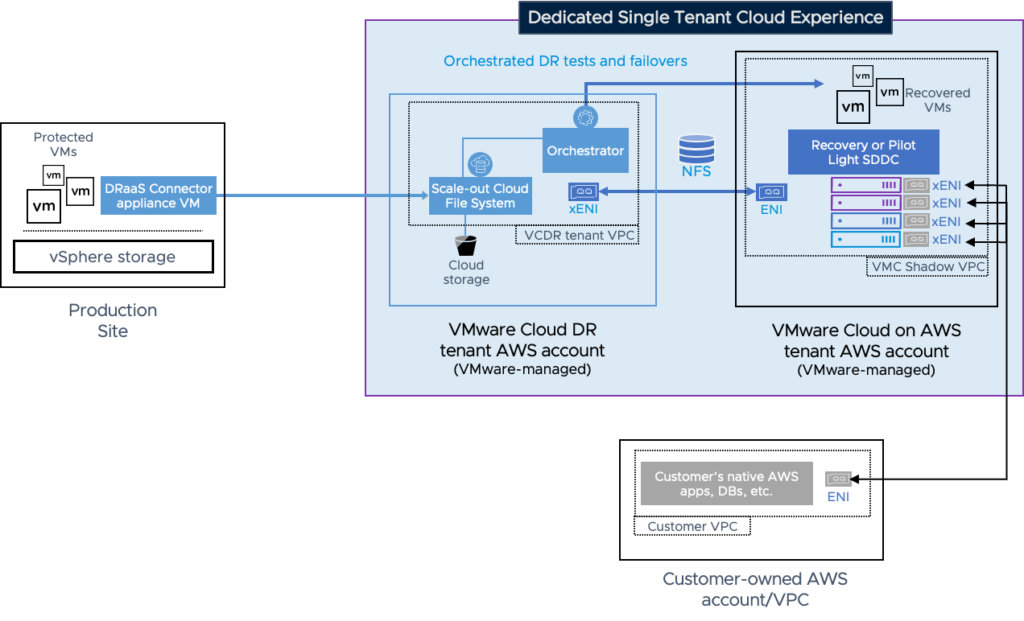
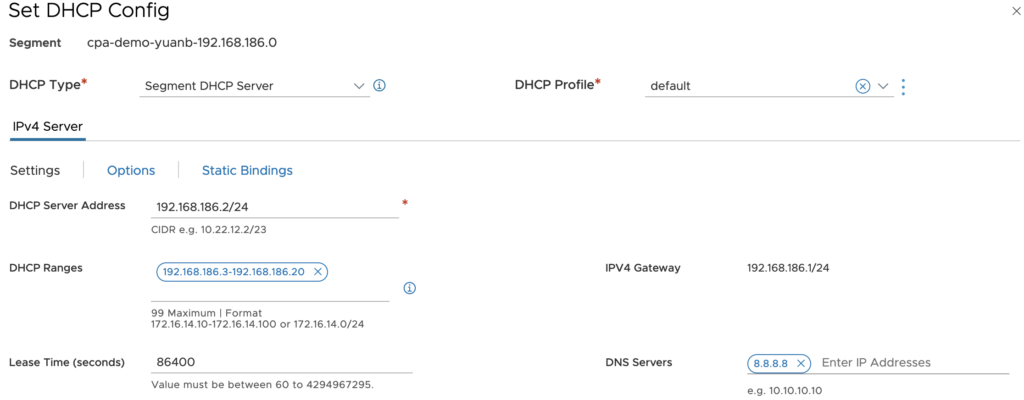
VCDR deliveries cloud service that protects on-prems workloads to VMC on AWS. It replicates VMs to cloud object storage called SCFS, in event of disaster event occurs, it recovers VMs on VMC on
AWS with on-demand mode. The warm and on demand DRaaS solution provides customers a low TCO and fast recovery capabilities with better RPO and RTO.
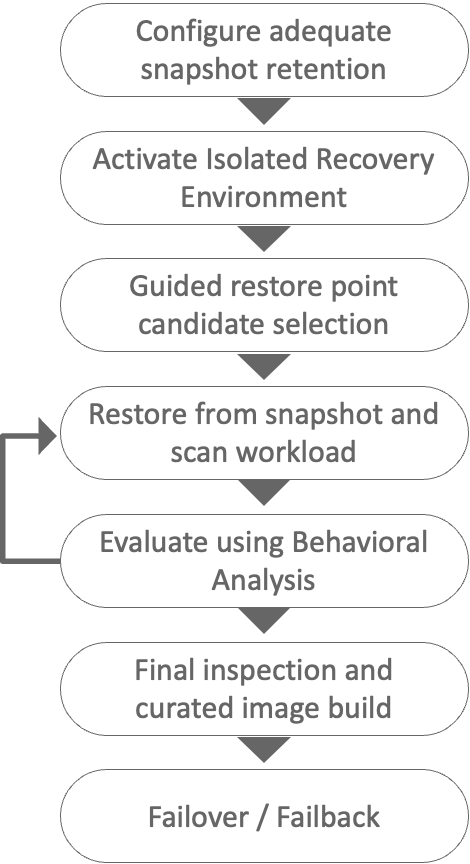
RWR is a build-in as-a-service ransomware recovery solution that extends existing VCDR to delivering the following capabilities like, air-gapped immutable cloud-based VMDK backups, guided ransomware recovery workflow, NGAV and behavioral analysis, VM network isolation in IRE (isolated recovery environment) and recovery point selection through VMDC change rate and file entropy etc.
The architecture components of VCDR and RWR includes following items,
- VMware Cloud on AWS: provides an on-demand SDDC that is used by DRaaS as a cloud DR target
- SaaS Orchestrator: DR orchestration components that runs in AWS to execute DR plans
- DRaaS Connector: OVA file VM installed in any on-premises vSphere to protect VMs which uses VADP to create snapshots of VMDK, and CBT to query VMDK change block
- Scale-out Cloud File System (SCFS): where vSphere VM backups are encrypted and stored that is based on AWS S3 to acts as NFS datastore allowing live-mount to boot VMs from SCFS directly
- Isolated Recovery Environment (IRE): restore the backup data to an isolated recovery environment (IRE) to contain and remedy ransomware before migrating back into a production environment
- NSX Advanced Firewall: create the desired network isolation
- Carbon Black Cloud: to inject the malware sensors into the VMs when being recovered into the IRE to provide improved capabilities against modern threats
- Next-Gen Anti-Virus (NGAV): to detect system vulnerabilities, known malware file signatures, and behavior analysis of running systems
Next, in this article I am going to show you how to configure ransomware protection and recovery using VCDR and RWR feature. The flow starts from creating protection group to take snapshot, then use recover plan to restore and evaluate using RWR, and finally to restore in SDDC of VMC on AWS.
Pre-requisite
Before starting to create protection group, a couple of things need to make sure that we may successfully conduct the recovery.
- Ensure the VM is installed the latest VMware Tools
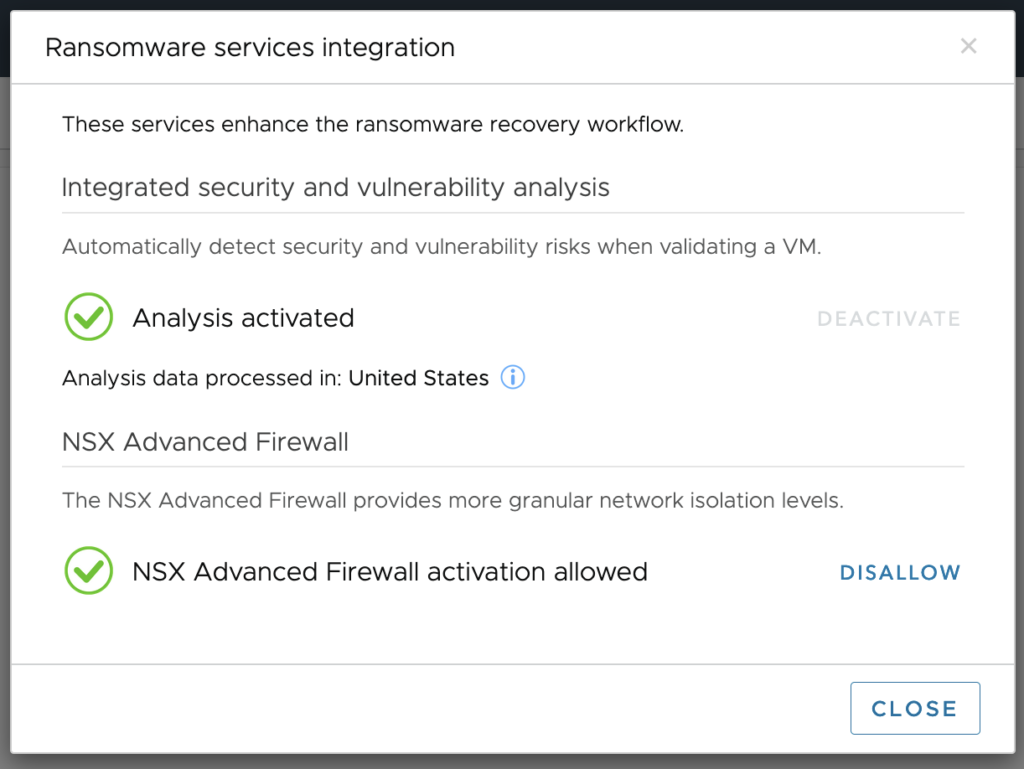
- Enable Analysis service and NSX Advanced Firewall in Settings
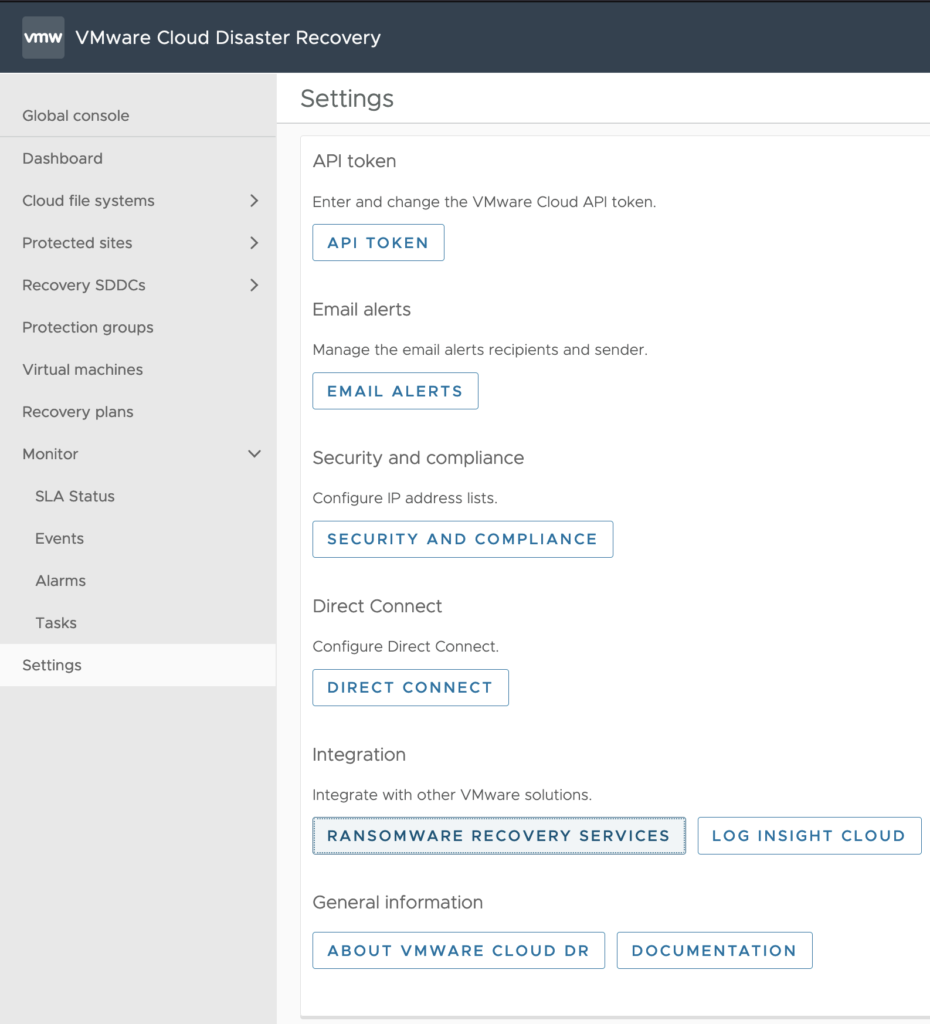
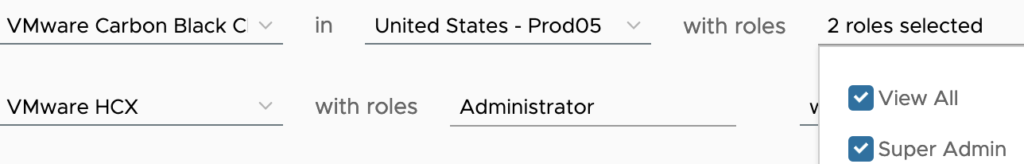
- Check the role of Carbon Black and VCDR in your VMware Org, for Carbon Black it should go with Super Admin, for VCDR the role should be Orchestrator Admin
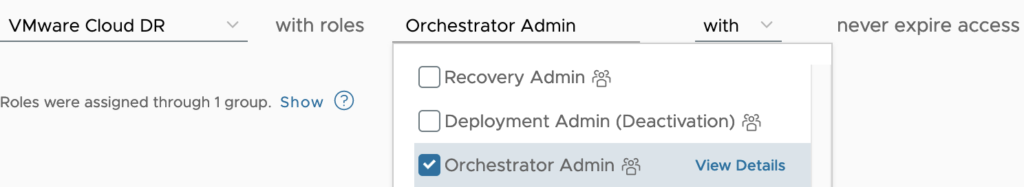
- configure DHCP for VMs’ vSphere distributed switch or NSX Segment in source and destination in order to make VMs can have IP address automatically when it is recovered in IRE
Architecture design
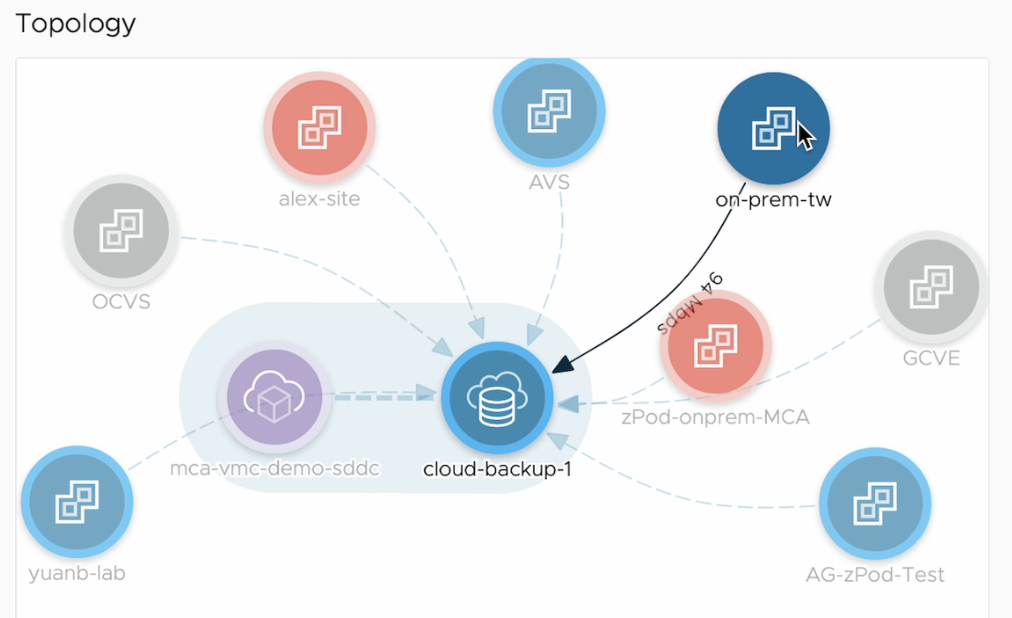
Here is the design of this deployment that VMs are in on-prem-tw site, which will be replicated to SCFS cloud-backup-1 and recovered in SDDC mca-vmc-demo-sddc.
As see in VCDR dashboard that on-prem-tw was already attached to cloud-backup-1 that is associated with existing SDDC.
Create protection group
We created a protection group named pg-tw-03
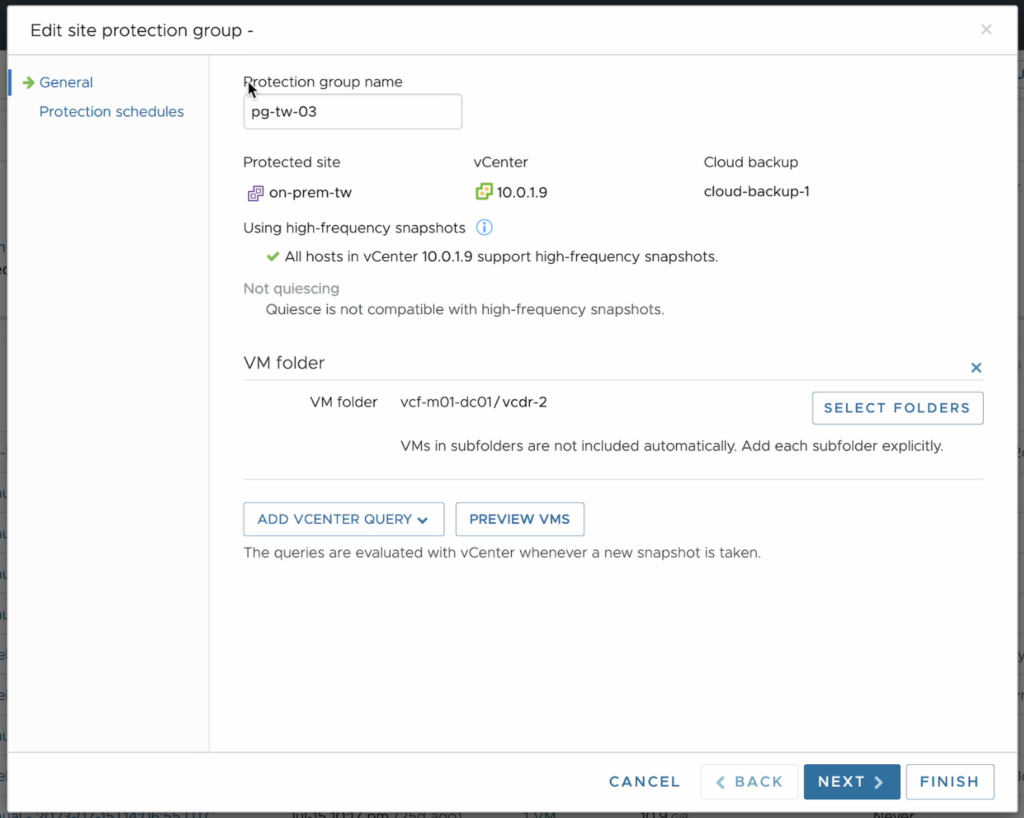
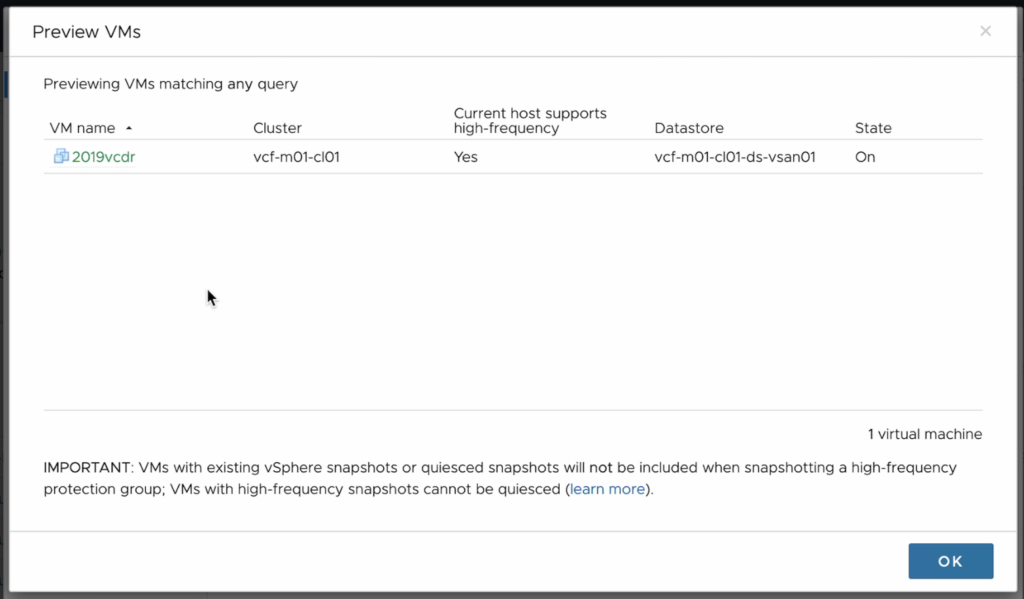
By assigning the VM folder it will query the active VMs in this folder and show you the result,
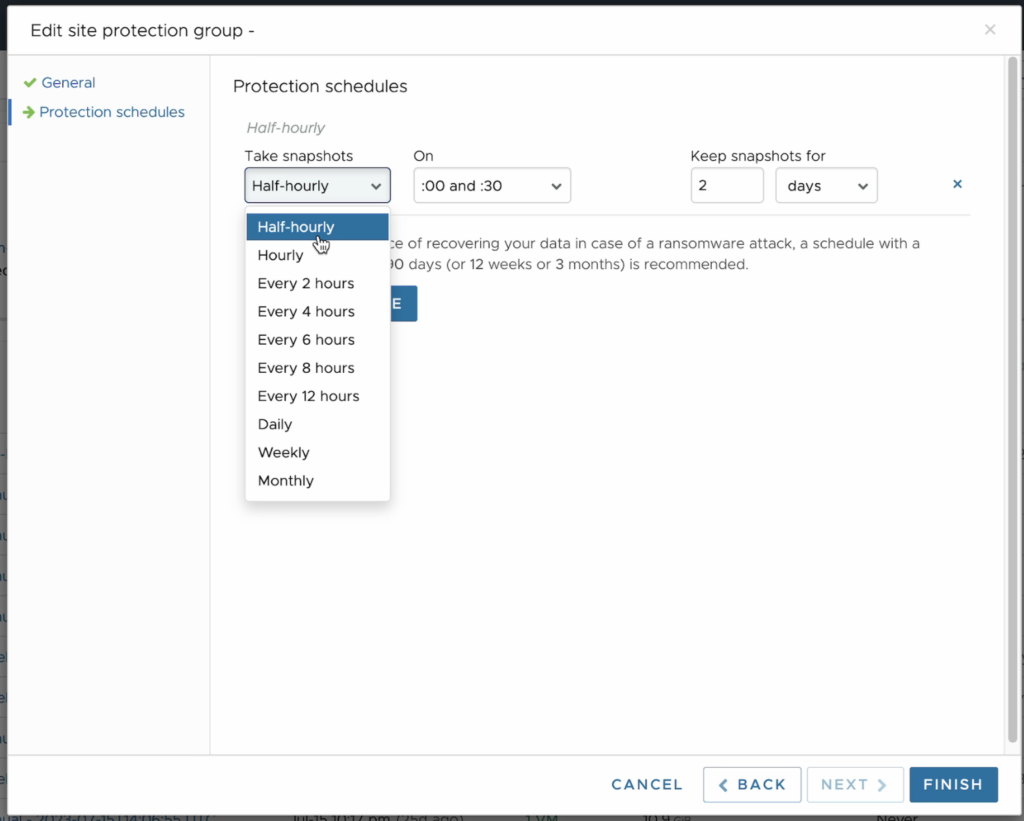
Backup schedule and retention was set half an hour and keep for 2 days.
Create Recovery Plan
In the step, we will match protect group created previously, and resource in vCenter of on-prems and SDDC respectively,
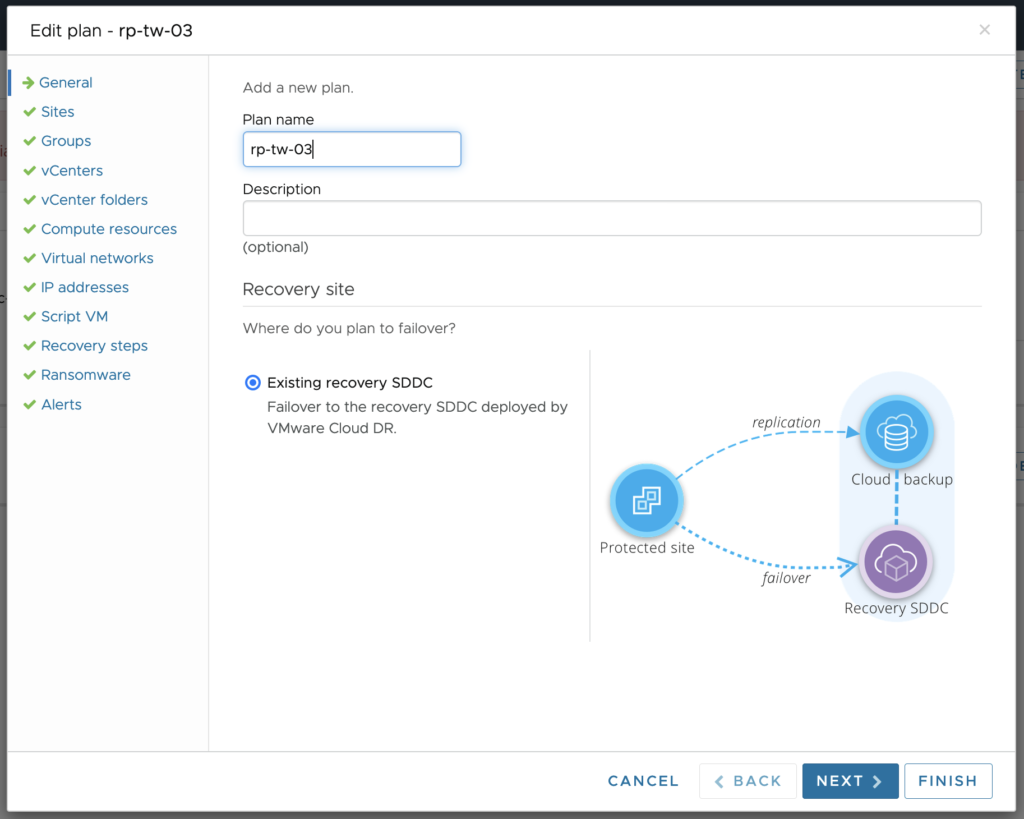
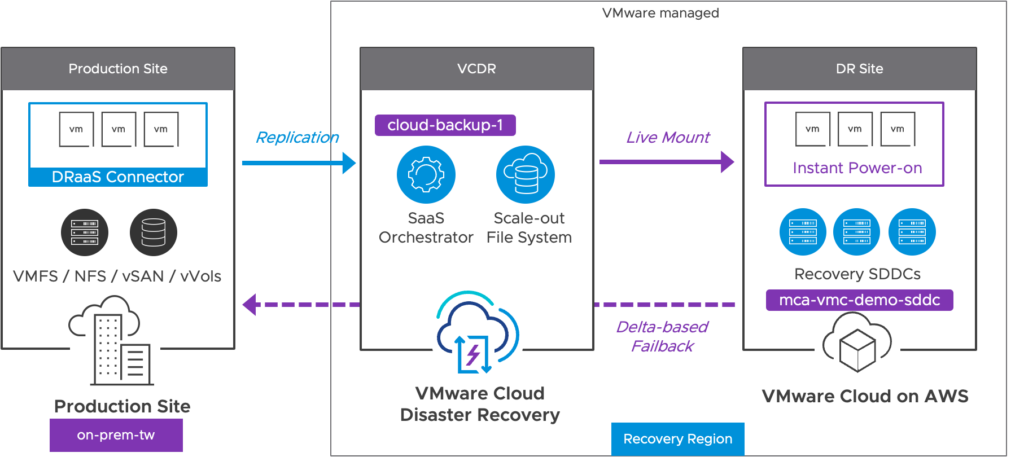
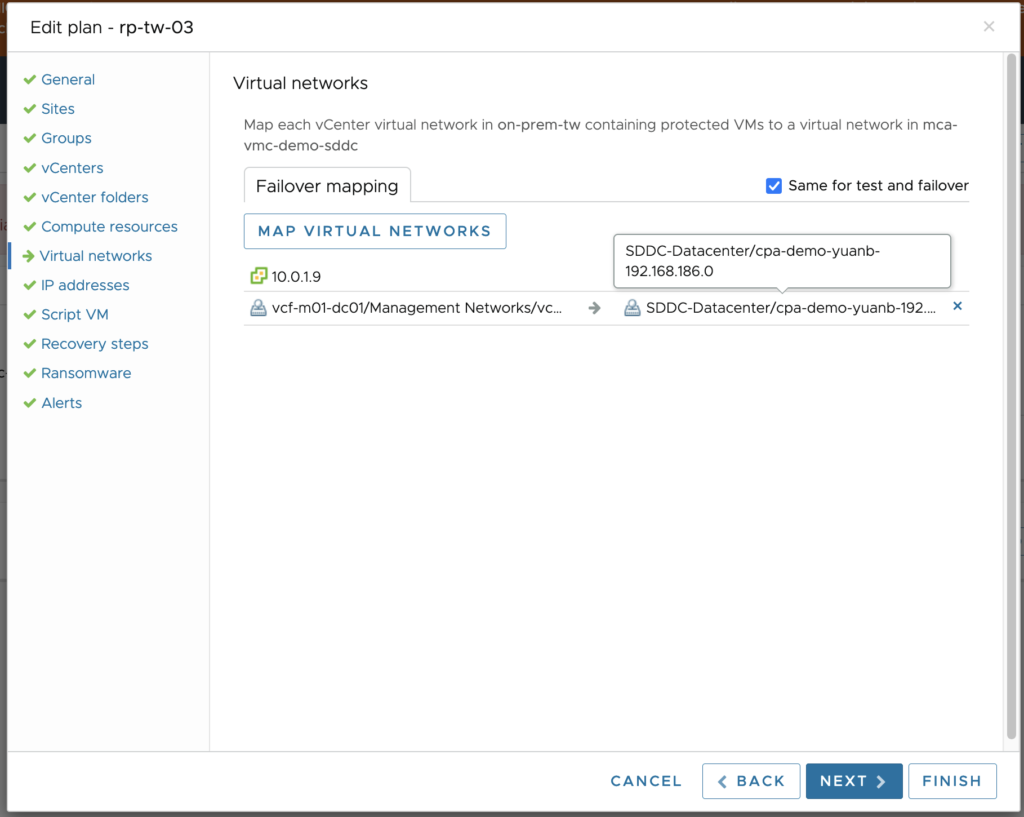
Need to highlight here in network part that we need to enable DHCP at both sides as stated above to for IP address assignment,
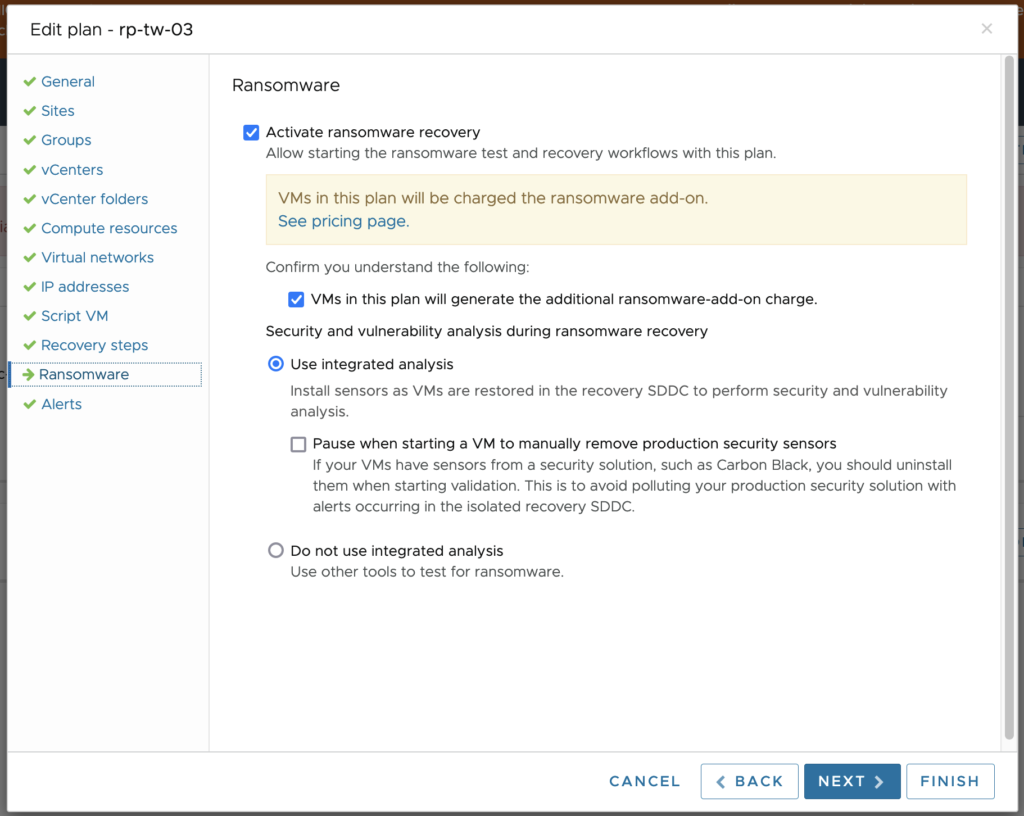
Here we check to activate ransomware recovery and confirm we understand charge will be applied for this service.
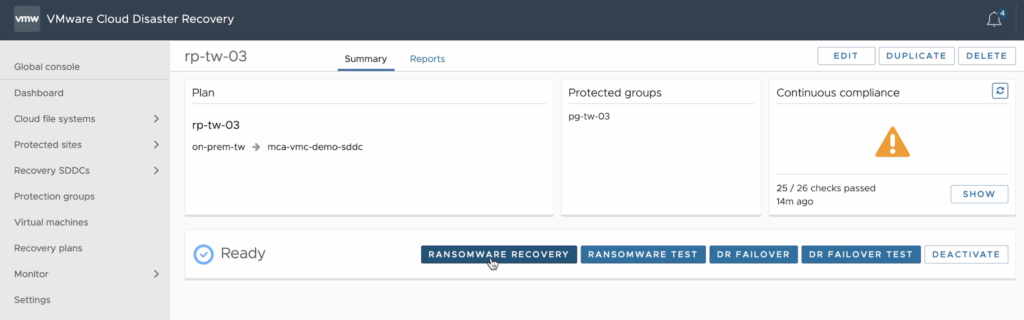
Ransomware Recovery
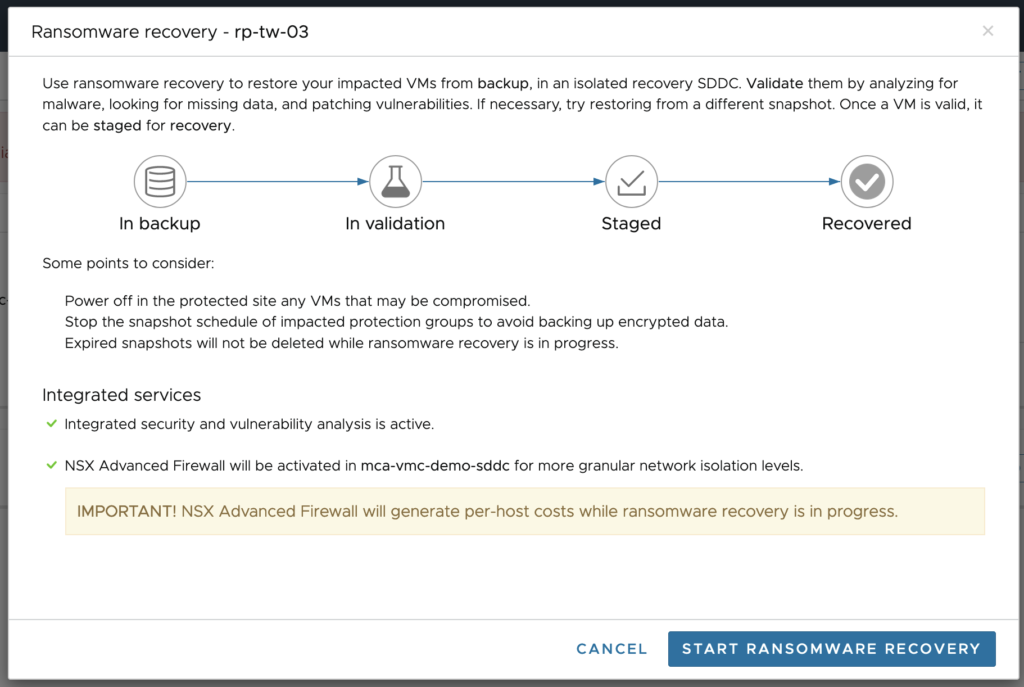
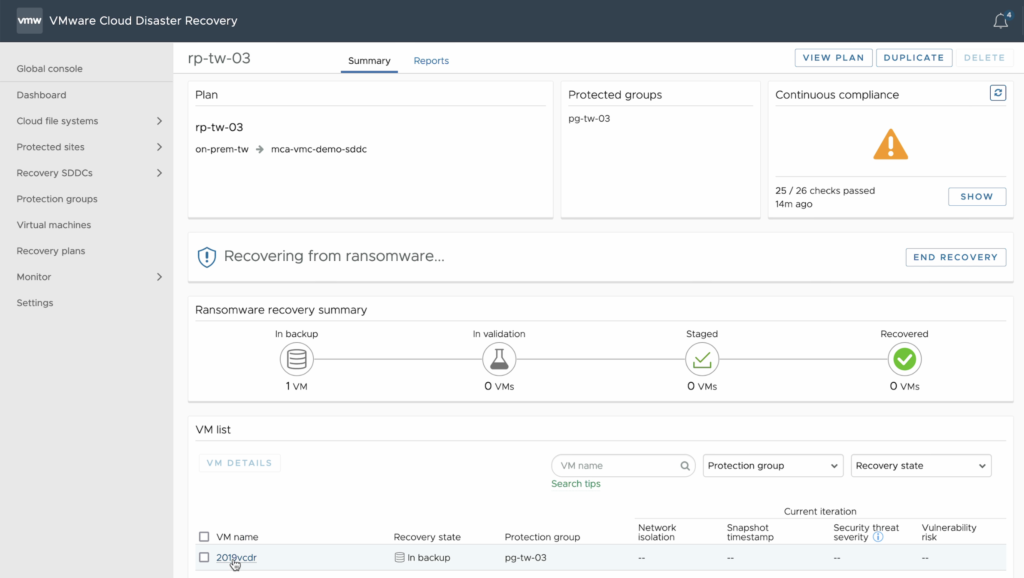
By clicking Ransomware Recovery button, the process will be initiated to choose an ideal snapshot to do the analysis. This includes four processes, backup, validation, staged and recovered.
Confirm to start,
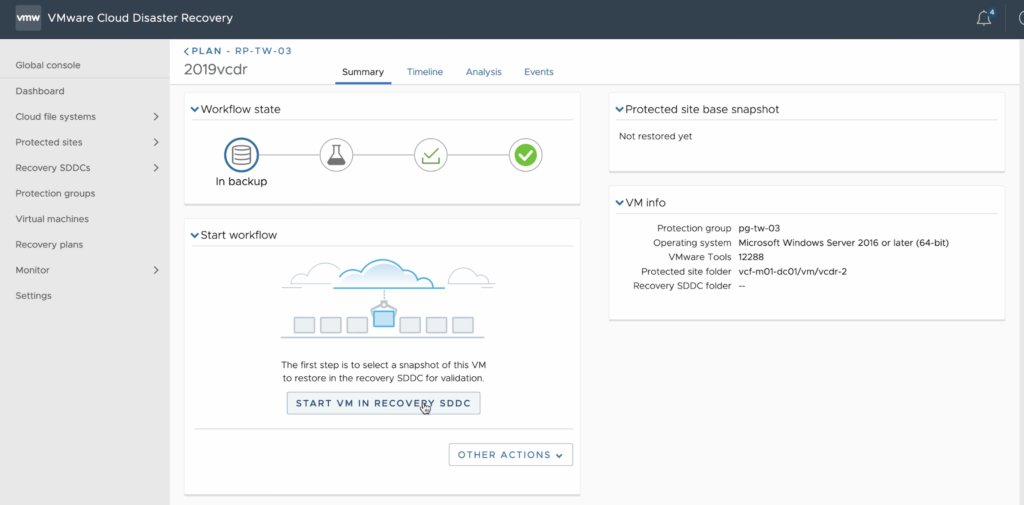
Next will configure to start the VM in recovery SDDC,
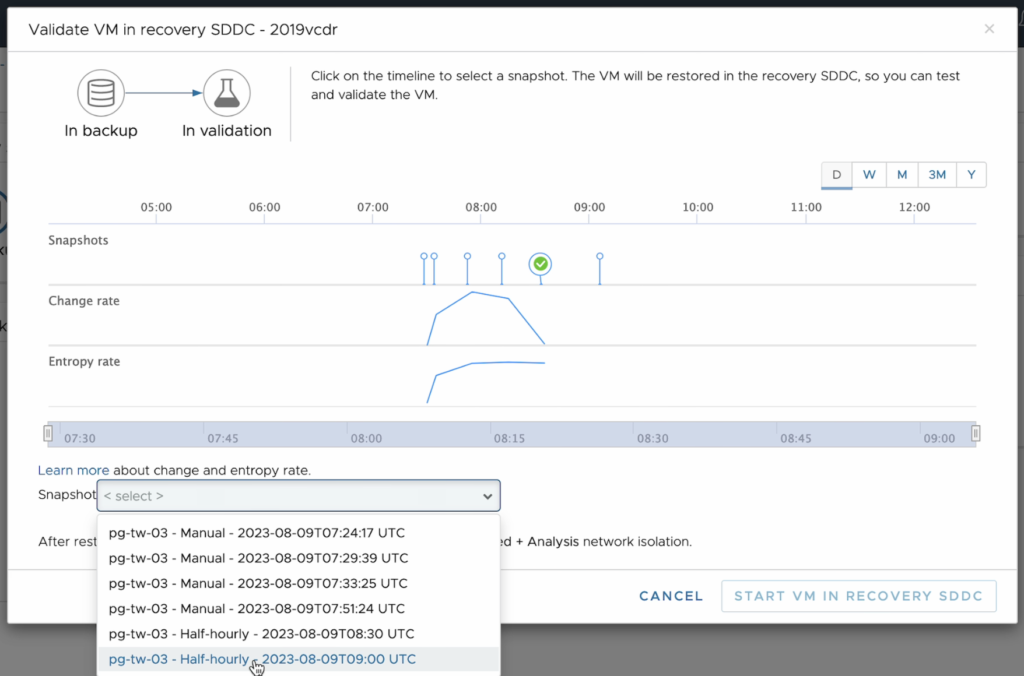
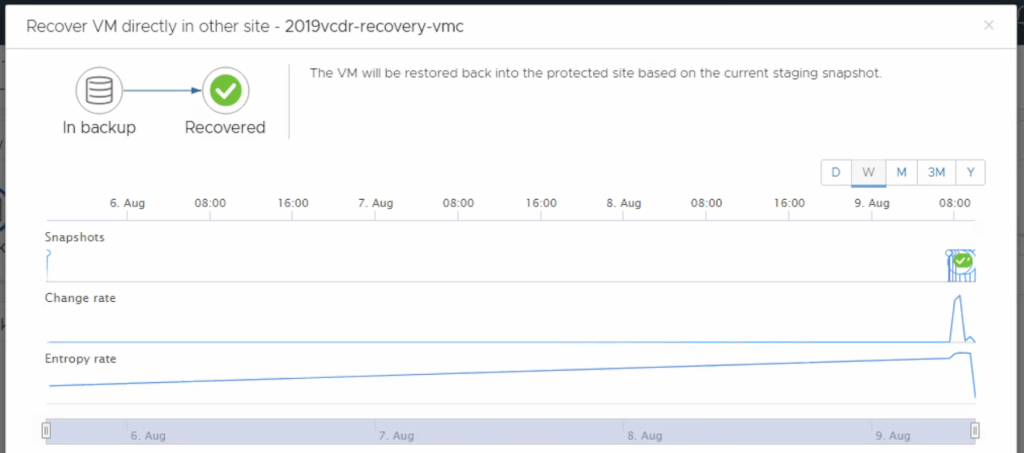
In the step to choose snapshot, VCDR provides diagram to show the change rate and entropy rate along the time which gives an idea to identify those snapshots taken before malicious attack. The Change rate measures the amount of changed bytes comparing previous vs new snapshot. The Entropy rate gives you a second measurement to observe VM or file change in case the graph change doesn’t consistent, say change rate is flat but entropy rate has obvious change, this indicates the VM might be encrypted that we need to skip it and look another one.
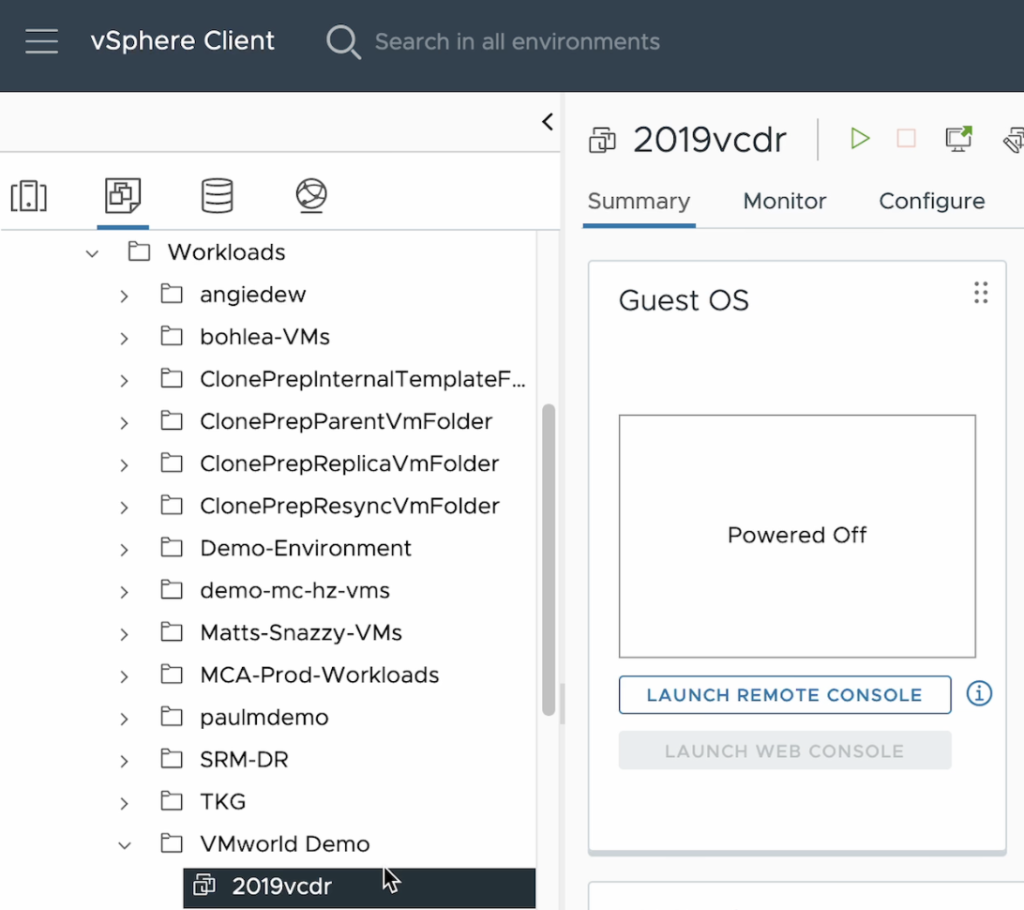
After choosing one snapshot, VCDR will quickly bring up this VM in target SDDC using live-mount. When we look into folder and will see the VM ‘2019-vcdr’ appears and start status is power-off,
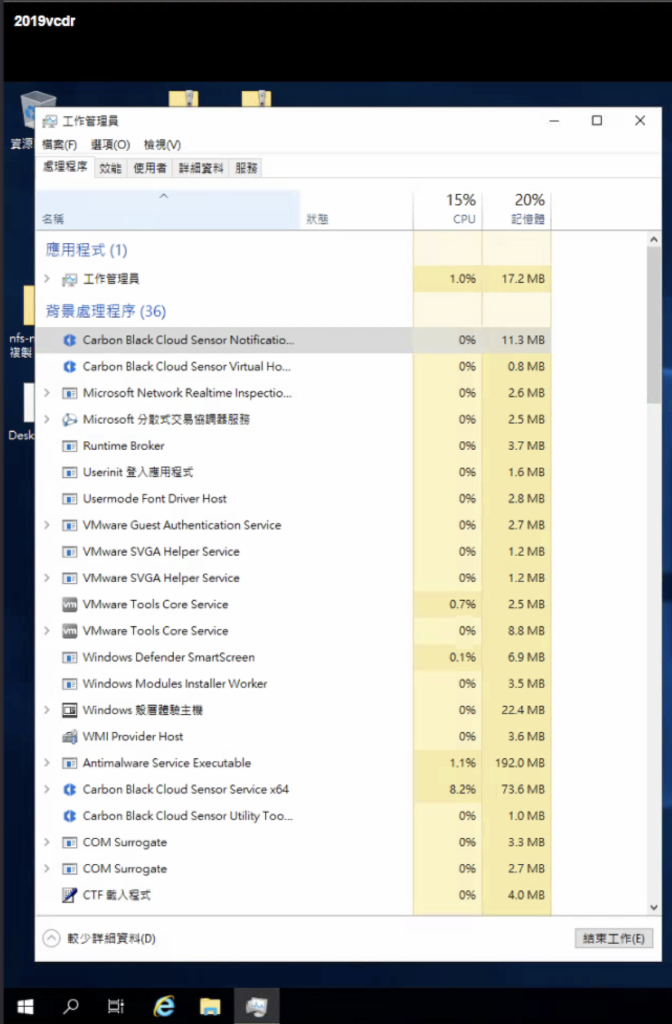
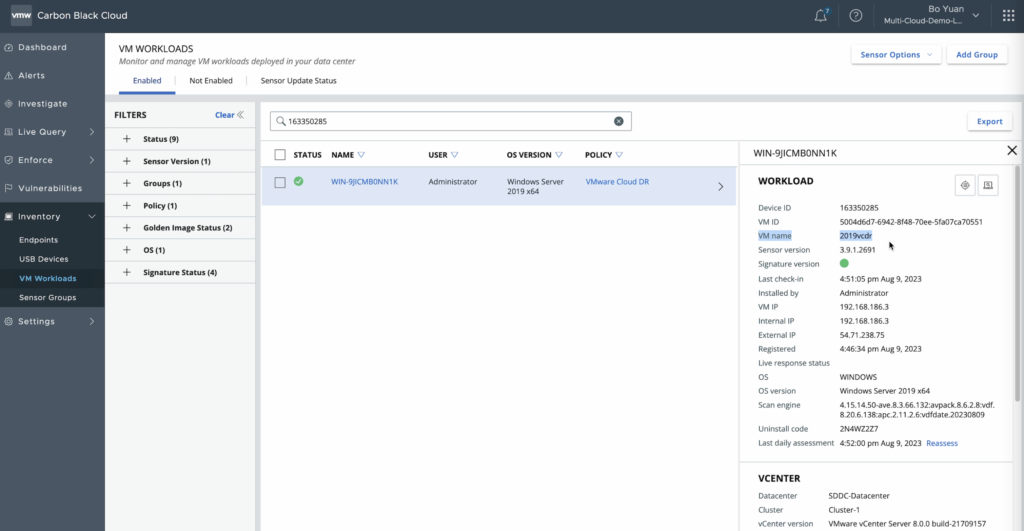
When the VM was powered on, through the VM console we can see agent of Carbon Black is being installed, and the VM will be reboot one time.
At the meantime of activating ransomware recovery, VCDR will create a few firewalls in NSX for different scenario that facilitate you to change policy of network isolation.
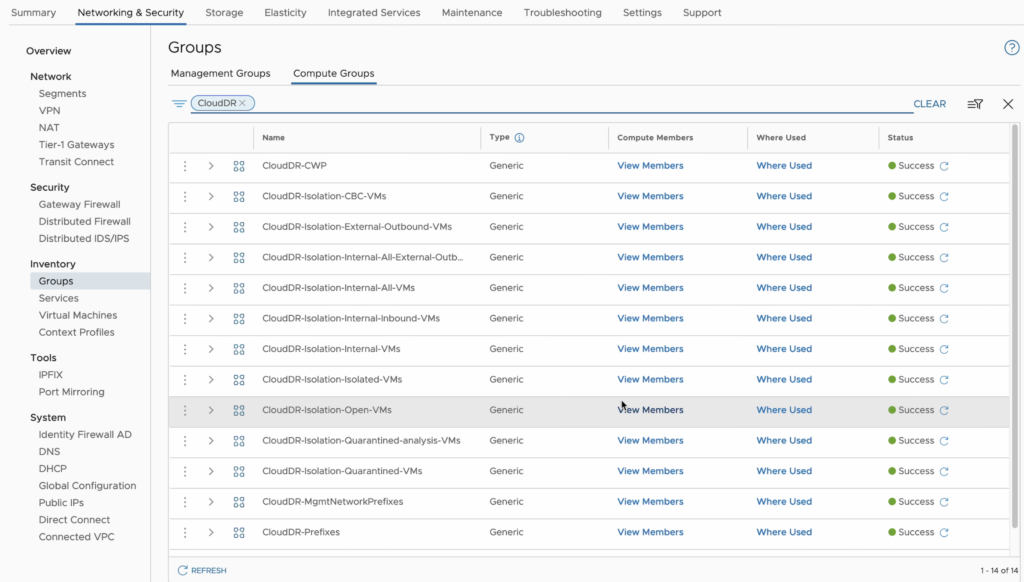
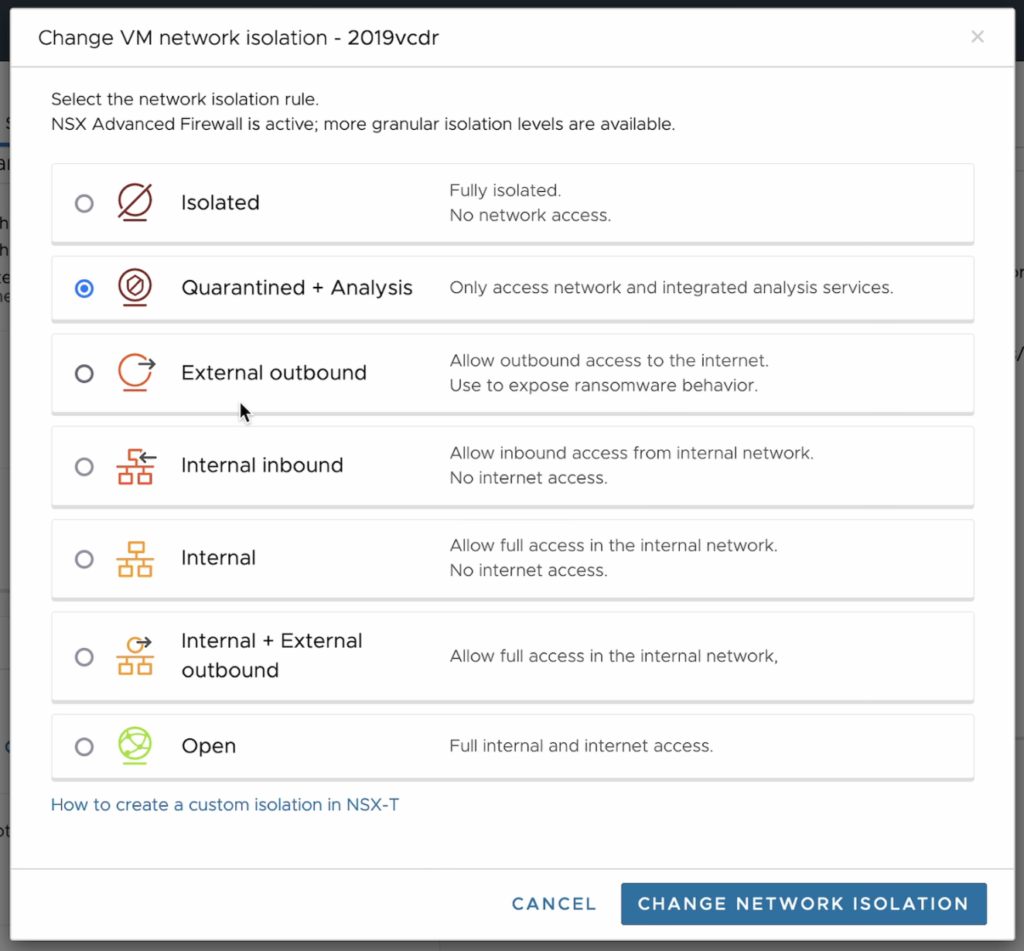
When VMs are in validation, they are first put into a ‘Quarantined+Analysis‘ network, which only allow VMs to connect over the internet to NSX-T Advanced Firewall for integrated security, and Carbon Black Cloud for vulnerability, and basic network services like DNS and NTP.
You can choose different network isolation levels for one or more VMs on the recovery SDDC, depending on your method of analysis and how much isolation you require.
We can further look into details in Carbon Black by opening in security console,
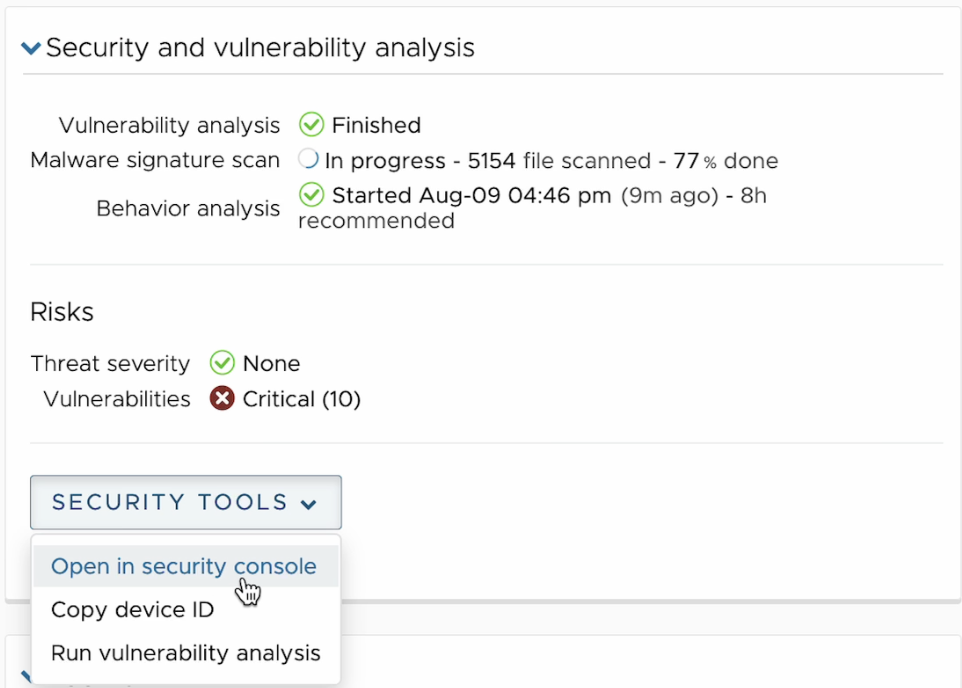
The analysis will be performed and minutes then you will see the report of vulnerability analysis, malware signature scan and behavior analysis. In my case all are green.
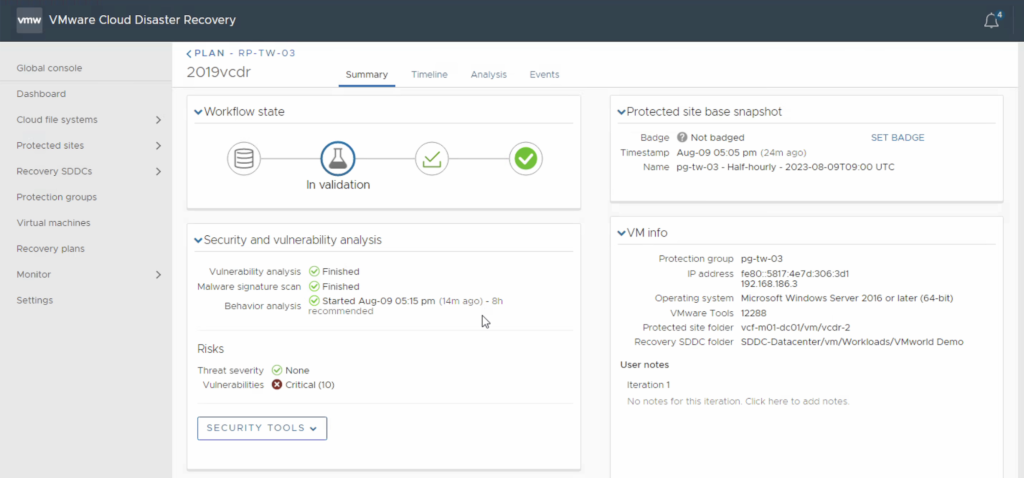
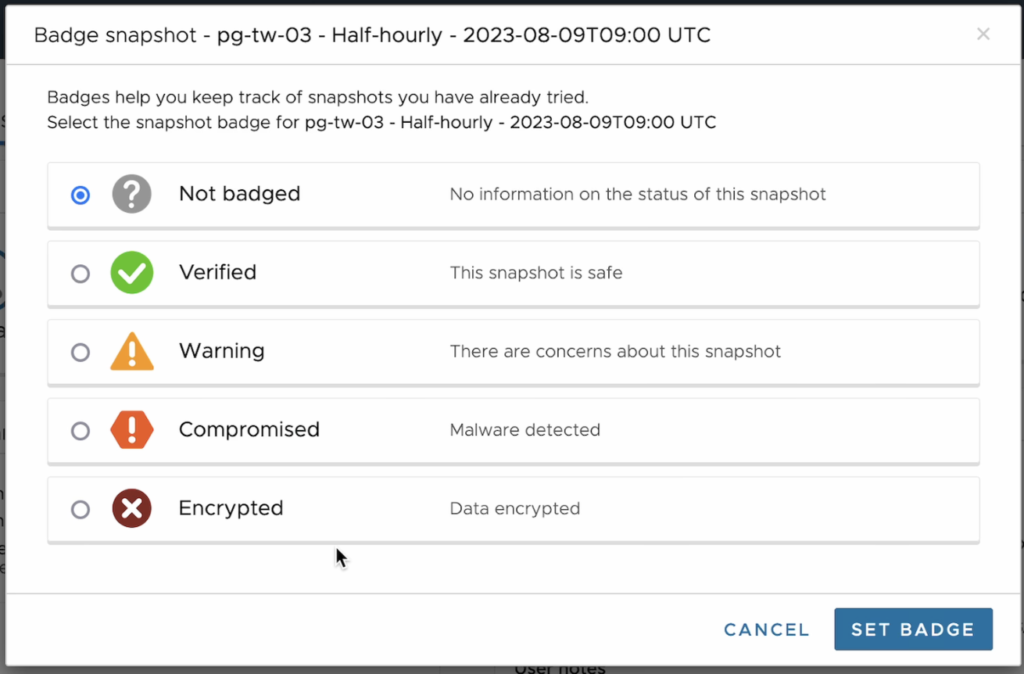
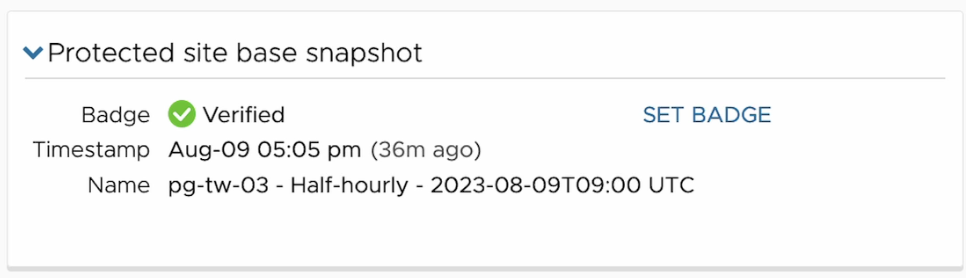
We may change the badge to verified to mark this snapshot with different badge to indicate health status for future use. In my case it passed the security and vulnerability analysis, I would mark it verified.
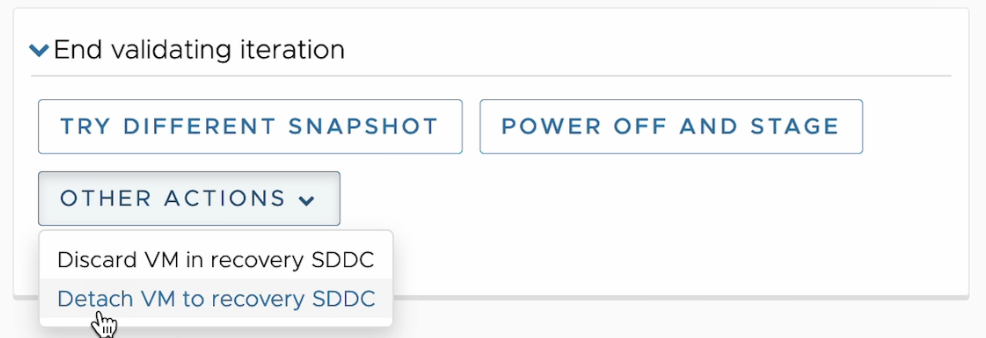
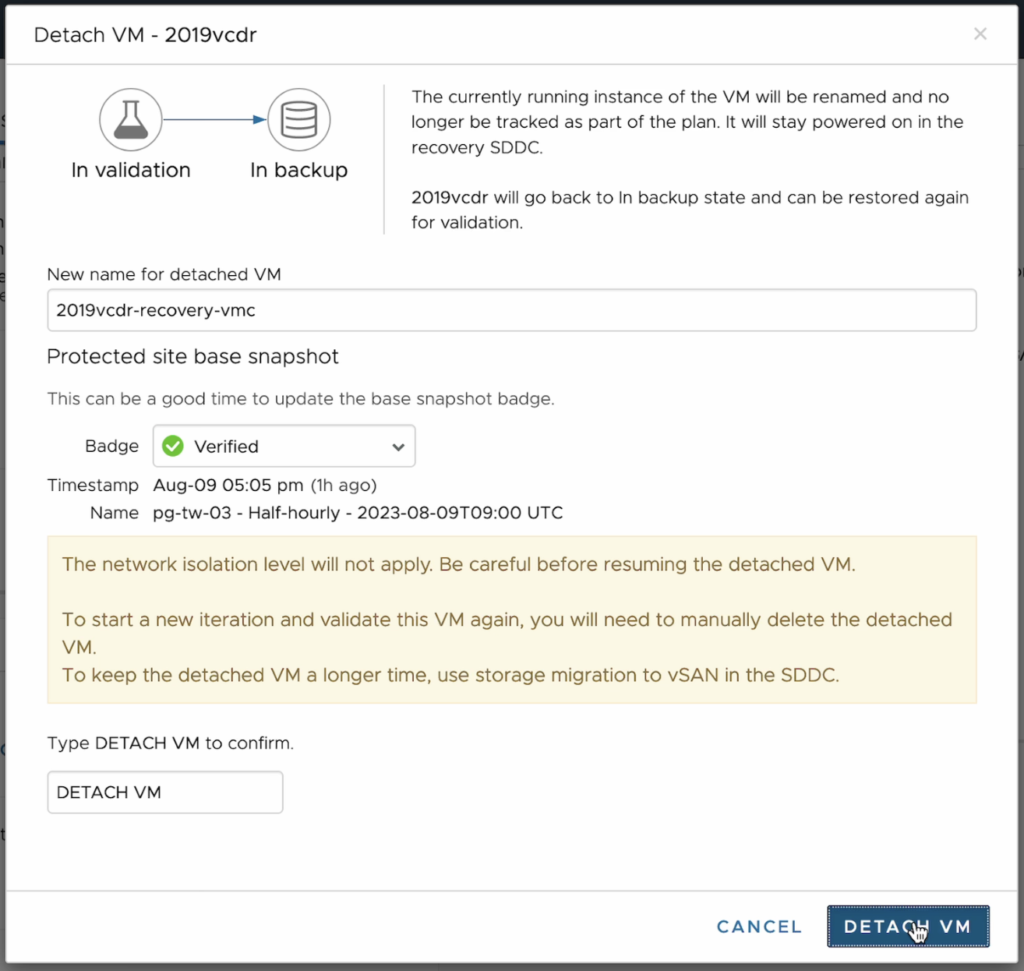
Recovery to SDDC
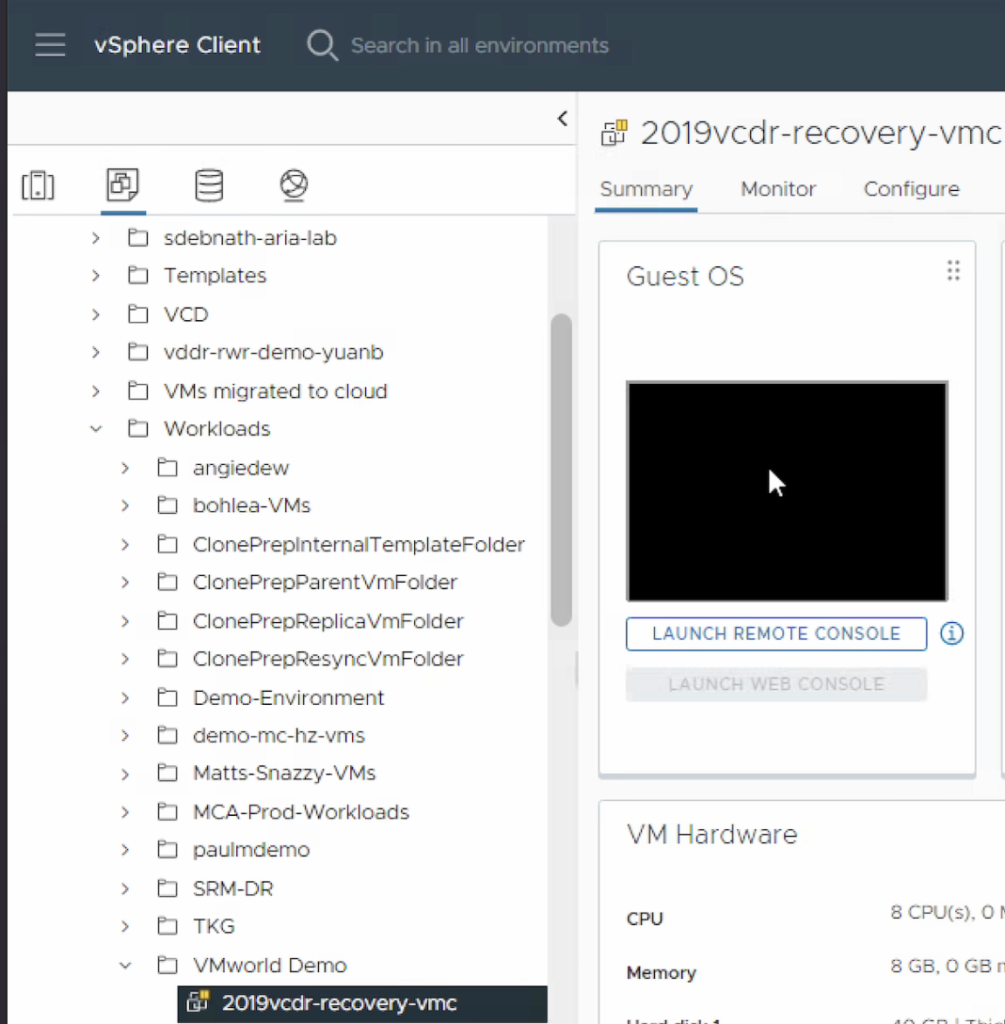
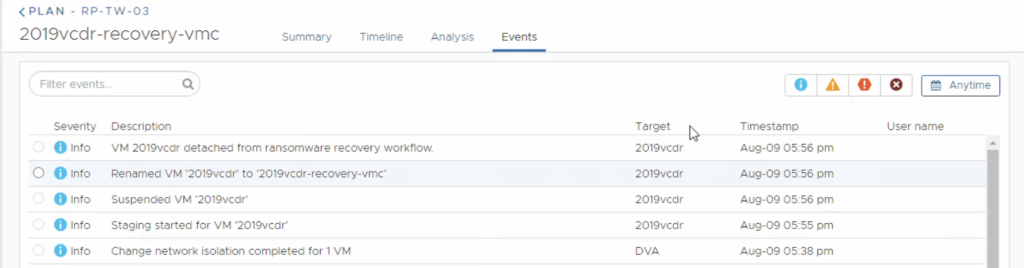
Finally we will recovery this VM to SDDC by detaching VM to recovery SDDC. We need to give a new name of this VM, here we name it ‘2010vcdr-recovery-vmc’
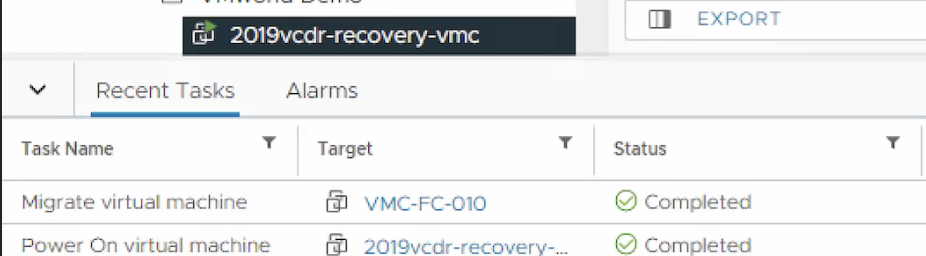
Returning to vCenter, the name of the VM has updated to new name we just gave. Sooner in status we observe that VM changed to Power-on status.
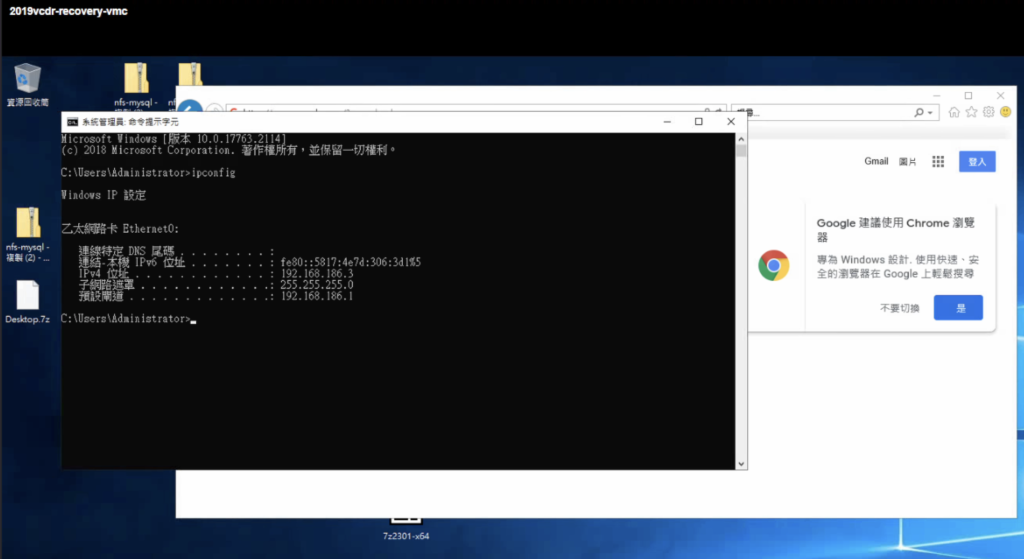
Enter the console we can see the IP address was assigned by DHCP and the VM is able to access internet.
In the VCDR it shows that status has changed from backup to recovered,
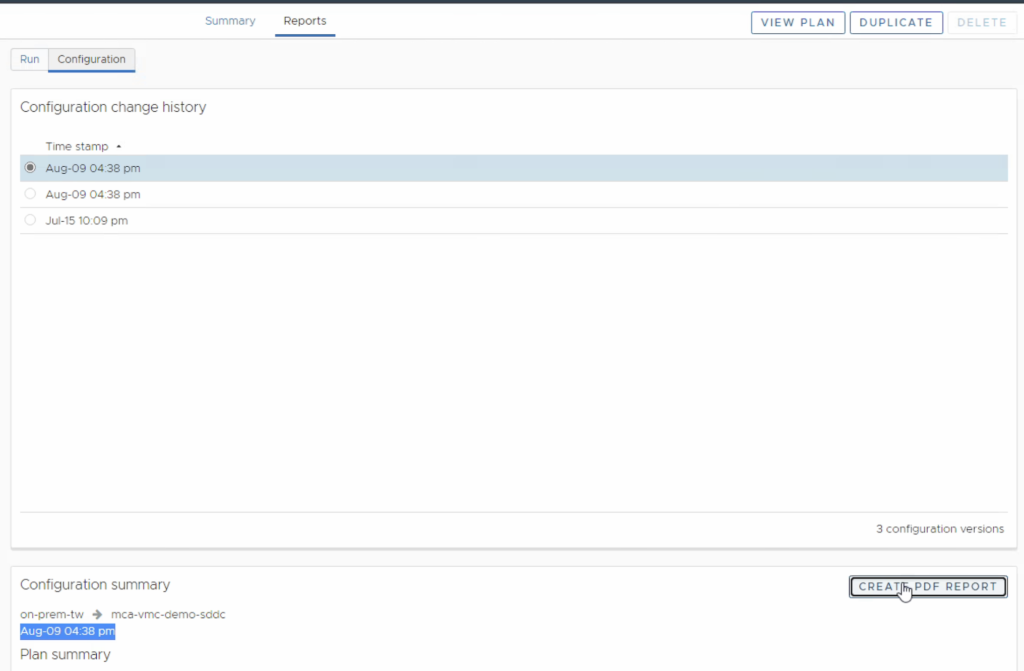
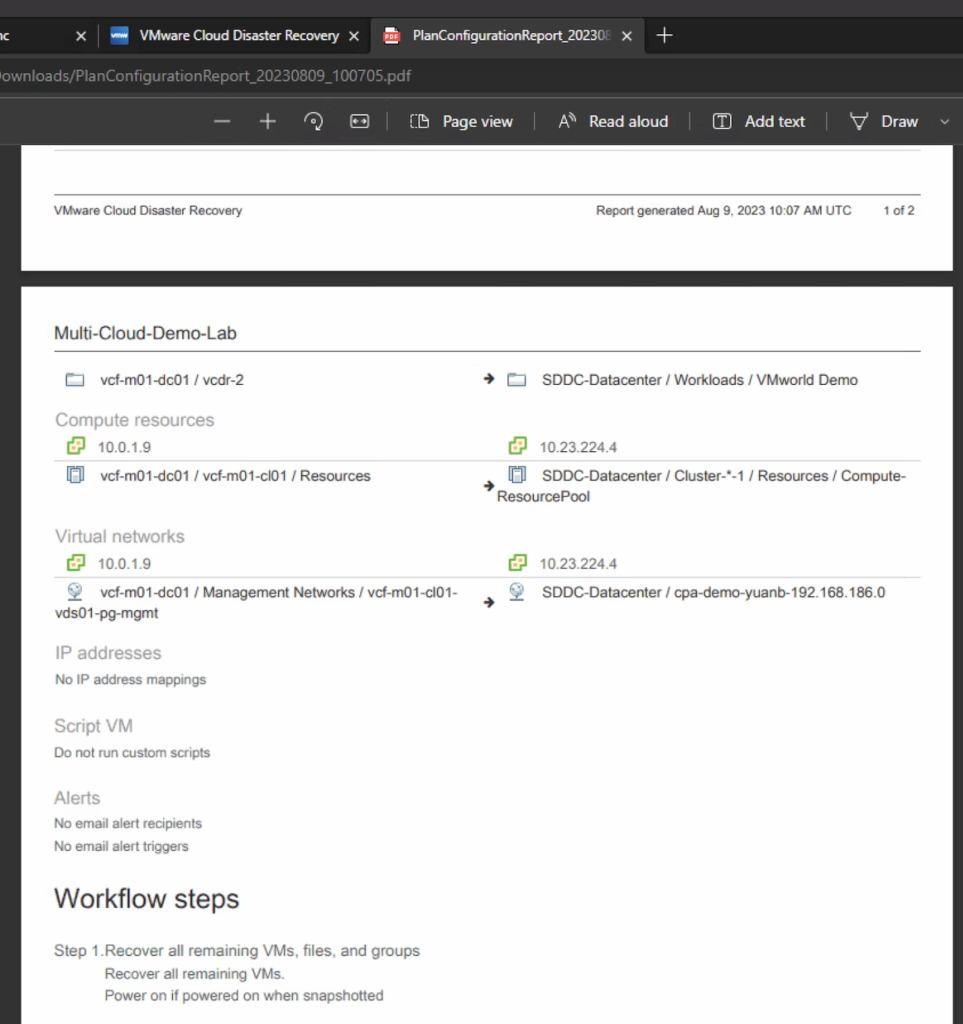
VCDR also provides comprehensive events to record activities during the recovery process. Also the report can be generated in a PDF file.
Conclusion
VMware Cloud Disaster Recovery with Ransomware Recovery is a SaaS based and on-demand disaster and ransomware recovery service that protects vSphere workload on-premises into the cloud. It leverages the execution and operational efficiencies of a single integrated data stack to automate and orchestrate all aspects of DR that you can use the recovery SDDC and IRE to perform analysis, remediation, and validation of compromised VMs without the risk of infecting other workloads in production.
